Raising awareness about IoT security, understanding the risks assumed from growing your network, and recognizing security measures to implement all can help companies reduce their IoT vulnerabilities.
As employees increase how often they use smart devices as part their daily jobs, businesses are investing in building internet-of-things (IoT) networks to keep their people and processes connected.
While IoT networks make information accessible and protected from hardware errors, businesses should invest in the proper tools to keep their information safe.
Over 20% of companies reported a data breach or cyberattack in 2018 that could be traced back to unsecured IoT devices, according to a Ponemon Institute Survey.
This article will focus on the approaches that help build a better security system and prevent a destructive breach.
Raise Awareness of IoT Vulnerabilities for Your Company
Many of the risks associated with IoT devices are distinct from other online security concerns.
Companies should invest time to learn how IoT devices could be putting their operations in jeopardy before deciding how to secure their network.
According to Forrester’s The State of IoT Security 2018, hackers’ motives may not be associated with financial gain. The report states that IoT hackers tend to form centralized groups with a defined purpose.
Hacking an IoT device could mean accessing confidential company information on a security camera, a connected printer, or supply chain machinery.
Because all devices in an IoT network are connected, these infiltrators can use this data to disrupt a company’s entire operations and demand payment to restore functionality to a factory’s machinery.
The More IoT Devices, The More Vulnerable Your Network
Each device in an IoT network represents an access point for hackers who may cross over from one device to another.
For example, in a casino data leak, hackers breached an aquarium’s temperature-control system to gain access to data about the casino’s highest paying customers.
The IoT temperature control device pictured below is not the device in question, but it illustrates how a smart thermostat uses WiFi to communicate with cloud servers.
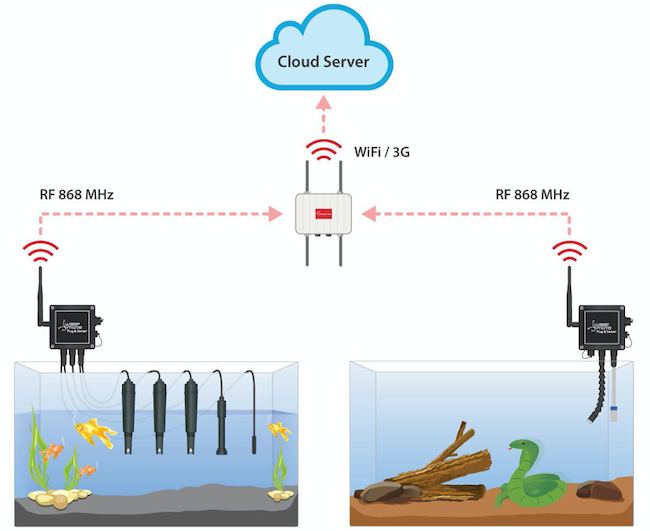
Source: libelium.com
According to a Business Insider report of the aquarium data leak, it’s becoming more and more common for hackers to target IoT devices like thermostats to extract confidential data.
Research Proactive Security Measures to Implement
Your company can proactively avoid some data security risks of IoT networks.
A few ways to strengthen your company’s IoT network include:
- Learning about your network architecture
- Partnering with a software development company with a track record of secure and successful IoT projects
- Leverage certifications
Get Smart About Your Network’s Architecture
Companies can use their existing network management tools to survey their network.
A typical IoT network is a dynamic system with many moving parts and access points: The devices and servers that make up a network represent access points that are connected to several areas where confidential can reside.
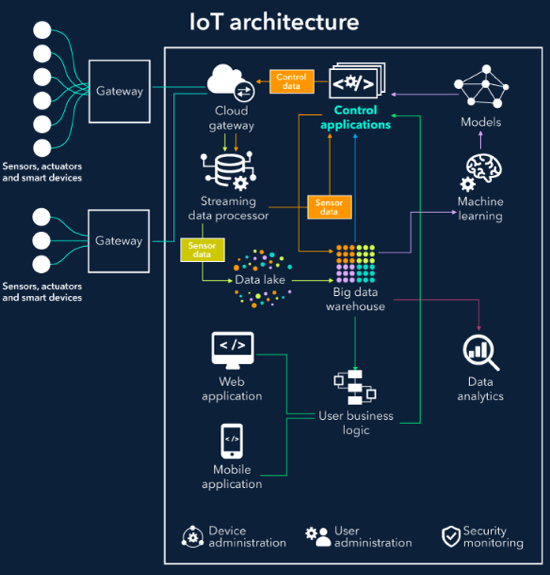
Source: scnsoft.com
If your company understands its network architecture, it can figure out how to separate sensitive IoT networks from business network as to prevent a harmful data breach.
Reviewing Suppliers’ and Vendors’ Security Protocols
The most common cybersecurity topics of concern affect the security of your IoT network: Who you allow to connect to your networks.
Beyond internal employees, your suppliers’ and vendors’ devices could facilitate a security breach at your company if they are connected to your network. Target’s security breach, for example, happened because hackers gained access to a third-party vendor’s unsecured HVAC system.
If your suppliers and vendors have IoT-enabled devices connected to your network, your network’s safety could be at risk.
If you work closely with other businesses, its a good idea to periodically survey your network with the goal of identifying atypical traffic patterns.
Leveraging Existing Certifications
In correlation with the rising IoT market, IoT data certification programs continue to emerge.
A reliable third party can monitor the authenticity of servers your IoT devices connect with and only allows connections with authenticated servers.
Checking with your suppliers and vendors to ensure they are using IoT security certifications is another smart safety measure.
Secure Personal Devices
You can also strengthen your individual device’s resistance to bad actors through a few different approaches
- Enable Two-Factor Authentication
- Implement Regular Updates
- Limit Secure Activity on IoT Devices
Enable Two-Factor Authentication
Two-Factor Authentication (2FA) confirms a user’s identity using more than just a password and protect an IoT product from impersonation attacks.
To this point, just 31% of businesses require two-factor authentication for connected devices. In a remote work environment, this number is far too small.
For example, a hacker would need to learn a user’s password and move past fingerprint, SMS message, or facial scan to gain access.
Beyond the security benefits, using a fingerprint or SMS message to confirm your identity is more efficient than entering log-in information.
If you forget your password, two-factor authentication allows you to quickly gain access to your device.
Implement Regular Updates
Establishing a consistent maintenance schedule where you catch and implement software updates is crucial to securing IoT devices.
IoT devices are prone to security breaches partly because they are more challenging to patch than laptops and servers.
Patch management is a growing industry that your business should remain aware of if it plans to allow IoT devices to access its network.
Limit Activity on IoT Devices
It’s important for employees to understand the risk their individual devices may bring to the office and make decisions accordingly.
If your company is deciding whether to opt for a smart printer, make sure the benefits outweigh the risks.
On an individual level, it’s worth considering the implications of connecting smart devices to applications such as banking or insurance accounts: While some businesses are accountable for their app development procedures, individuals may not be. Implementing a policy that limits the use of connected devices to highly-secured networks can reduce risk from personal error.
Awareness is the first step toward prevention when it comes to IoT data breaches.
Learn Ways to Protect Your Company’s Data in an IoT System
IoT security is necessary to safeguard both your business and your personal life from potential hackers.
Proactive measures to secure your data could include restructuring your network’s architecture, adopting an IoT certification program, or simply taking steps to secure your personal devices.
Your business should consider the risks seriously and then take action.